Kaspersky Technologies
Learn how our technologies work and how they enhance your security
Watch our video
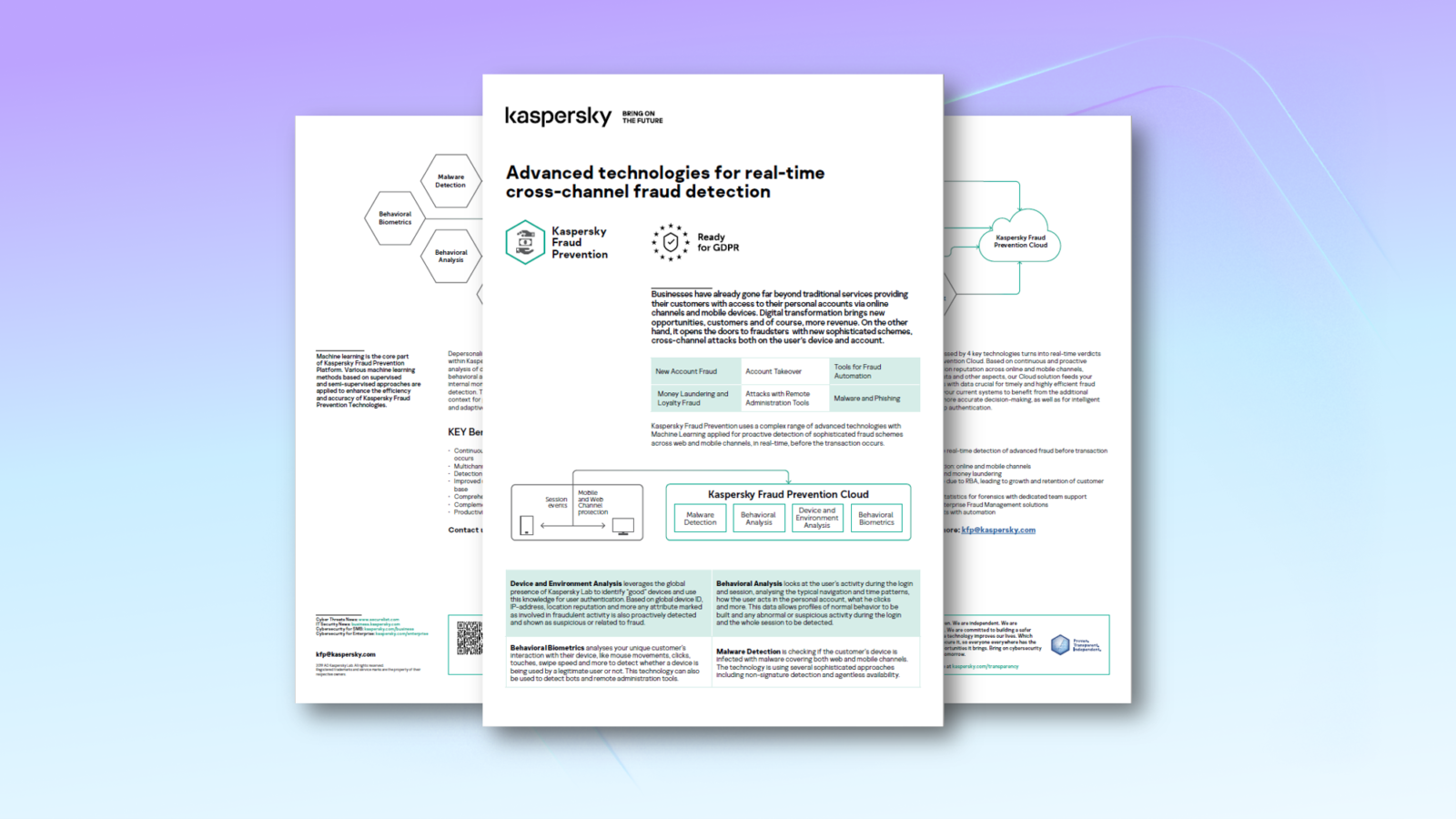
Behavioral analysis
Looks at the user’s activity during the login and session, analysing the typical navigation and time patterns, how the user acts in the personal account, what he clicks and more.
This data allows profiles of normal behavior to be built and any abnormal or suspicious activity during the login and the whole session to be detected.
Behavioral biometrics
Analyses your unique customer’s interaction with their device, like mouse movements, clicks, touches, swipe speed and more to detect whether a device is being used by a legitimate user or not.
This technology can also be used to detect bots and remote administration tools.
Device and environment analysis
Leverages the global presence of Kaspersky to identify “good” devices and use this knowledge for user authentication.
Based on global device ID, IP-address, location reputation and more any attribute marked as involved in fraudulent activity is also proactively detected and shown as suspicious or related to fraud.
Malware Detection
Agentless malware detection checks if the customer’s machine is infected with malware without any additional
software installed on the user side.
This information is used to determine the legitimacy of transactions, as well as for Risk Based Authentication and Machine Learning modelling.
Useful Resources
Useful Resources are made to give your more information on what we do
Advanced Fraud Prevention Technologies Datasheet
Principle fraud risks for the digital businesses
News & Updates
Latest news in the field of fighting online fraud

Common spear-phishing tricks
Virtually every employee of a large company comes across the occasional e-mail aiming to steal their corporate credentials. It’s usually in the form of mass phishing, an attack in which e-mails are sent out at random in the hope that at least some recipients will take the bait. However, the stream of phishing e-mails may

How GDPR changed the world, and privacy regulation’s future
One piece of regulation has never before had such global impact as the EU Global Data Protection Regulation (GDPR.) It’s firmly established data privacy in the public mind, giving extensive and unassailable rights and affecting behavior well beyond the EU’s borders. GDPR legislation was a pioneer that other regions followed. The California Consumer Privacy Act (CCPA)

A focus on greater transparency and accountability
With information technologies inseparable from modern society, the importance of cybersecurity is growing, and therefore, trust has never been more important. Clients and partners of companies working in the field of information security need to understand who is involved in protecting their confidential data, what information they are sharing with whom, their guiding principles, and

6 antiphishing tips
What do e-mails with headings “You’ve won a million dollars” and “Your account is blocked” have in common? They’re almost always signs of a scam. Their aim is to convince the recipient to follow a link to a phishing website and enter confidential information: login and password or bank account details. Here’s how to spot

Remote dating: How do the apps safeguard our data?
The pandemic and the restrictions that came with it have led to an increase in the popularity of dating apps. For example, the total number of swipes on Tinder increased by 11% last year, with the daily number of swipes surpassing the 3 billion mark for the first time as early as March 2020. This is hardly

Why people fall for social engineering and how business can stop it
A security system is only as strong as its weakest link. And when it comes to cyberfraud, the weakest link is all around you: People. The easiest way for a fraudster to get what they want is to manipulate someone into giving it to them. For example, using a ruse to convince someone to give

Do cybercriminals play cyber games in quarantine? A look one year later
Last year, we decided to take a look at how the pandemic influenced the gaming industry and what new threats gamers could be facing. What we found was that, with the transition to remote work and remote learning, the number of blocked attempts to visit malicious game-related websites or follow malicious links from legitimate game-related

RIP, CAPTCHA
In a panel discussion at RSA Conference 2021 about Web attacks and online fraud, researchers discussed lessons drawn from studies of cybercriminal tactics and attacks on large organizations. One speaker, former law enforcement officer Dan Woods, talked about his experience training as a CAPTCHA farm worker. The work was copious and the pay meager (about $3

Phishing returns to its roots
Between tech support requesting access to your computer, concerned tax services specialists demanding payments, medical equipment suppliers “returning your call,” and many more — none legitimate — it’s a wonder anyone even answers their phone anymore. You’d be hard-pressed to find someone who hasn’t experienced some form of phone scam, although the name for it

Breaking the money mule’s back
In any bank fraud scheme, the criminals need to move funds to clean accounts or cash them out, and that means laundering. To cover their tracks, they transfer funds, first to money mules and thence somewhere else. At RSA Conference 2021, representatives of several major US and Australian financial institutions held a panel discussion on the topic of money mules and

Kaspersky Fraud Prevention and Indacoin Limited celebrate a year of successful cooperation
One year ago, a unique project Kaspersky Fraud Prevention became an important element of the security system of one of the pioneers in the field of a fiat-to-crypto exchange, which provides an opportunity to purchase cryptocurrency with Visa&Mastercard bank cards Indacoin Limited. After integration of the technology, the efficiency of the Indacoin Limited security system

COVID-19 vaccines in darknet marketplaces
In December of 2020, the US FDA approved the Pfizer vaccine against COVID-19. Within 24 hours, one of the largest global vaccination campaigns in history kicked off, with countries around the world rushing to begin the end of the pandemic. Unfortunately, supply chains haven’t been able to keep up, and poorly designed vaccination programs have resulted in long delays. And,
Request
a demo
We are sure there is nothing better than solving the real-world issues. Get in touch with us.
